Software Testing
The Quality Policy is deployed by way of a well-written and practical Quality Management System (QMS). Training on QMS is mandatory for all role holders in R.M Infotech (P) Ltd. We perform quality assurance and testing (including both unit and integration testing) as part of our application development and implementation services. We also offer quality assurance and testing services to our customers for their own products.
RM Infotech provides the following end-to-end services in the QA/Testing domain:
1. Application and Web-based testing 2. Component/ Structural testing and API testing 3. System testing 4. Regression testing 5. Security testing 6. Developing test strategies, test plans, and test cases 7. Manual or automated test execution 8. Automation test development using suitable tools that best fit your needs 9. Stress, load, performance, and usability testing 10. Maintaining test metrics, test harness, etc 11. Localization and Internationalization testing
Institutionalized Frameworks exist for key quality initiatives:-
1. Measurement centric approach to project management 2. Technology and Process Improvement 3. Defect Prevention 4. Competency building and deployment 5. Quality Training 6. Best Practices identification and deployment 7. New Quality Models 8. Lightweight processes
R.M Infotech's Process Performance model includes setting targets and measuring against the organizational targets. Over a period of time, R.M Infotech has developed it's prediction/forecasting model for efforts and defects. Projects attempt to uncover the targeted number of defects before committing a delivery to the client. Our historical data demonstrates an estimation accuracy of 85 percent and schedule slippage under 5 percent and Acceptance testing defects at 0.03 weighted defects per function point. Clients therefore, have a low risk of outsourcing software development to R.M Infotech (P) Ltd.
The domains in which RM Infotech has expertise are:
-- Banking & Financial Services,
-- Datacom & Telecom,
-- Pharmaceuticals,
-- eLearning,
-- Travel & Hotel
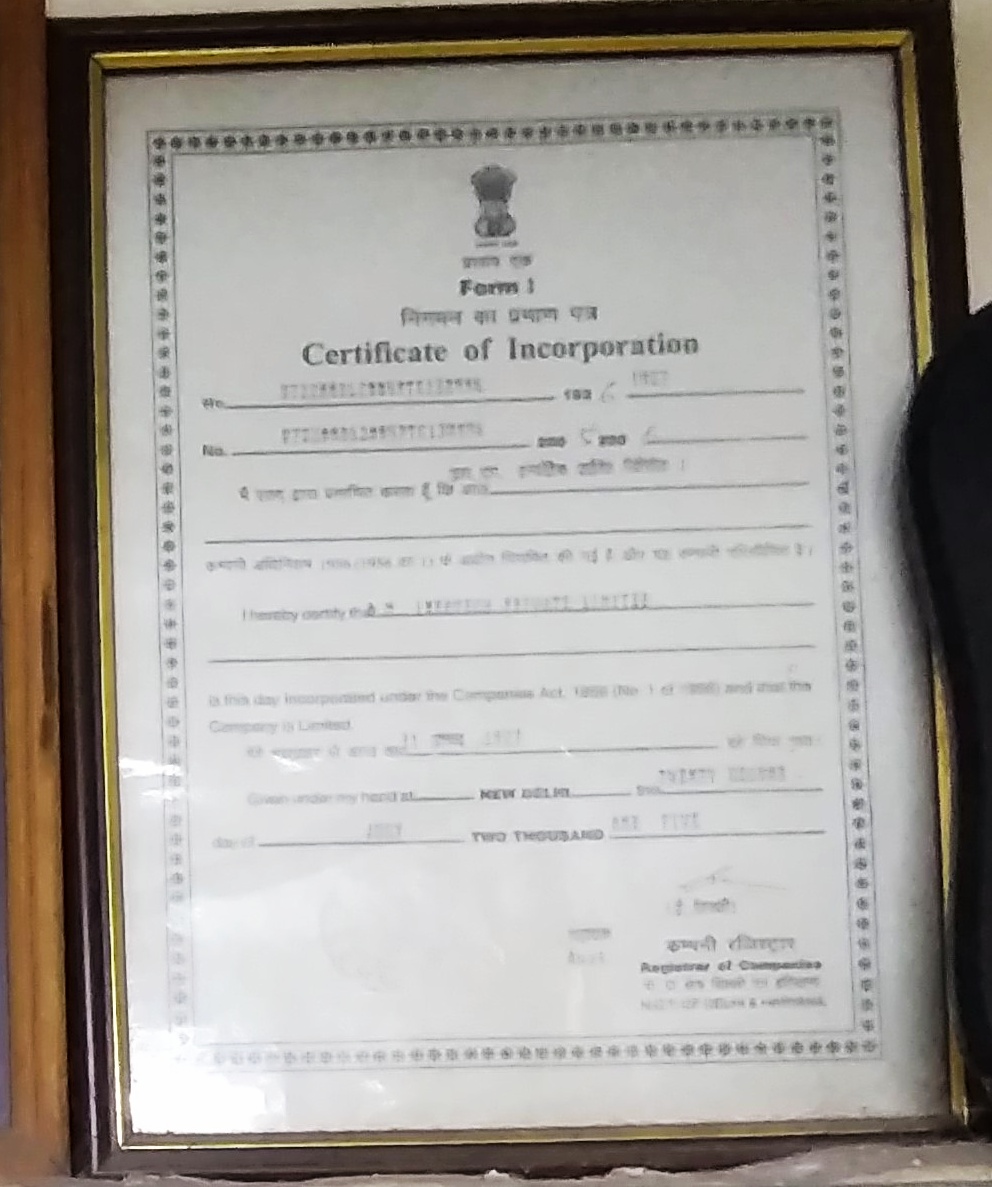
R.M Infotech (P) Ltd started a formal quality journey with a certification for ISO-9001:2000 in 2005. We at R.M Infotech Pvt. Ltd. is committed to follow all international QM Standards of ISO Certification for end user satisfaction.
Security Assessment Methodology
"There are number of steps to assure a company's security—firstly check all its controls (procedural controls, administrative controls, technical controls etc). The second step is to move into attack mode and check if every control, procedure, or product is configured or implemented properly. The third step is to do an audit." "We first do an internal audit for the company.Then an external threat is simulated by our experts. We have Certified Ethical Hackers to simulate internal and external threats
Vulnerability assessment Methodology:
Step 1 : Study & scope the IT architecture & components for assessment Step 2 : Determine the boundary of analysis Step 3 : Identify asset owners & schedule tasks Step 4 : Impact analysis for Active scans, which includes assessment of Service(s) or Server(s) scans in online production. Step 5 : Plan for Downtime & Contingency, if applicable Step 6 : Estimate the scan process, based on the complexity of the target network(s) and host(s) Step 7 : Define the scan Policy for each target. Scan Policy to define the level of scan - Information gathering, Policy checking, Port scanning, Password analysis, Attack stimulation etc. Step 8 : Scan the targeted network(s) and host(s), based on the defined scan policy Step 9 : Collect the scan results and analyze for security loopholes, configuration errors, default installation settings, overlooked setups, password quality, firmware/software revisions, patch fixes, security policy violations etc. Step 10 : Submission of Assessment Reports with suggestions and recommendations to fix the vulnerabilities
Security lapses or vulnerabilities:
1. Security threats and risks are not analyzed prior to selection of security technology and design 2. Corporates fail to deal with the awareness and operational aspects of security 3. Lack of robust security policy definition or non-adherence to security policies 4. Absence of non-periodic security audits of IT infrastructure and operations 5. Lackadaisical implementation of physical security - Easy physical access to Data centers & critical IT assets 6. Misconfiguration of servers - Default options in installation procedures of operating systems and applications, which can be hacked easily 7. Password User accounts with No Passwords or Weak Passwords - Leads to password cracks with easy guesses 8. Failure to block unauthorized access to application ports - Unwanted TCP ports are open in Application Servers 9. Lack of availability of data foot prints due to non-existent or incomplete logging and backup of data 10. Improper Virus prevention procedures - Lack of timely update of periodic virus signatures



Google Map - Locate Us
Gallery